Welcome to your comprehensive guide on secure mobile content solutions in Canada! Whether you’re a business owner, an IT professional, or simply someone concerned about digital security, this guide is designed to offer you actionable advice, real-world examples, and practical solutions to secure your mobile content effectively.
In today’s digital age, mobile devices have become integral to our professional and personal lives. With this increased reliance comes the challenge of securing sensitive information against cyber threats. This guide will walk you through essential steps to protect your mobile content, address common pain points, and provide best practices to ensure your data remains safe.
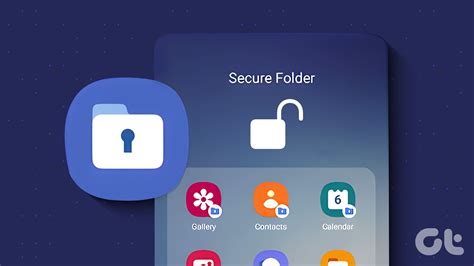
Understanding the Problem: Why Secure Mobile Content Matters
Mobile devices are gateways to a wealth of personal and corporate data. From emails and financial records to proprietary business information and confidential client details, these devices hold sensitive data that could be devastating if compromised. Cybercriminals are constantly evolving, making sophisticated attacks on mobile devices easier than ever. Protecting your mobile content is not just a safeguard; it’s a necessity to maintain your privacy and safeguard your business’s integrity. Here’s why securing your mobile content is critical:
- Preventing data breaches that could expose sensitive information
- Ensuring compliance with data protection regulations
- Maintaining trust with clients and stakeholders
- Avoiding legal repercussions and financial losses due to security failures
Quick Reference: Key Action Items for Mobile Content Security
Quick Reference
- Immediate action item with clear benefit: Enable two-factor authentication (2FA) on all accounts—it adds an extra layer of security beyond just a password.
- Essential tip with step-by-step guidance: Regularly update your device software. Navigate to your device settings, find the software update section, and ensure it’s enabled to automatically receive security patches.
- Common mistake to avoid with solution: Using public Wi-Fi networks for sensitive tasks—opt for VPNs to encrypt your data and protect against potential eavesdropping.
Detailed How-To: Implementing Two-Factor Authentication
Two-factor authentication (2FA) is a critical step in securing your mobile content. By requiring something you know (like a password) and something you have (like a code sent to your phone), it significantly reduces the risk of unauthorized access.
Here’s how you can implement 2FA:
- Choose a Reliable 2FA Method: Apps like Google Authenticator, Authy, or hardware tokens such as YubiKey offer robust 2FA solutions.
- Enable 2FA on Your Accounts: For each account, go to the security settings. Look for the option to enable 2FA and select your preferred method. Follow the prompts to complete the setup. You might need to enter a verification code from the 2FA app or provide additional information.
- Backup Options: Always set up a backup method in case you lose access to your primary 2FA device. This might involve receiving backup codes during setup or setting up a recovery method via email or a secondary phone number.
- Testing: After enabling 2FA, test logging in to ensure everything works correctly. This will help you understand the process and troubleshoot any issues that may arise.
Remember, 2FA is not foolproof but it’s a substantial step in bolstering your mobile security.
Detailed How-To: Keeping Your Device Software Updated
Regular updates to your device’s operating system and apps are vital for maintaining a secure environment. Updates often include critical security patches that fix vulnerabilities and protect against new threats.
Here’s how to ensure your device remains up-to-date:
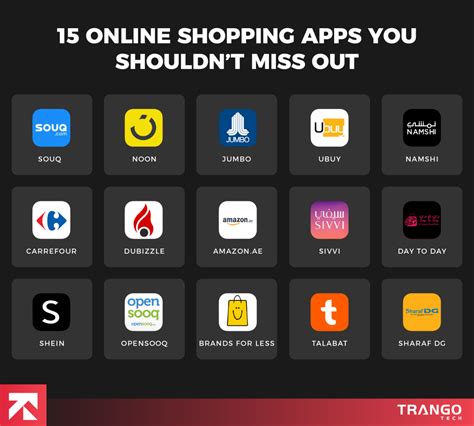
- Enable Automatic Updates: For iOS, go to Settings > Software Update > Automatic Updates. For Android, navigate to Settings > System > Advanced > Software Update > Enable auto-updates. This ensures your device always has the latest security patches.
- Manual Checks: Even with auto-updates enabled, it’s wise to manually check for updates periodically. Go to Settings > Software Update (iOS) or Settings > System > Advanced > Software Update (Android) to look for any pending updates.
- Check App Updates: Open the App Store (iOS) or Google Play Store (Android) and tap on your profile picture or icon in the top-right corner. Scroll down to see a list of available app updates. Tap Update All to ensure all your apps are current.
- Understand What Updates Include: Before updating, it’s good to know what’s included. Look at the release notes for any new features or security fixes that are being addressed.
Keeping your software updated is an ongoing process that takes just a few minutes but offers immense security benefits.
Practical FAQ: Answering Your Common Questions
What should I do if I suspect my mobile device has been compromised?
If you suspect a compromise, take the following steps immediately:
- Disconnect from any networks and turn off data services.
- Change all your passwords, especially for critical accounts.
- Run a comprehensive antivirus scan on your device.
- Consider wiping the device if the infection seems severe and restoring from a known clean backup.
- Contact your IT department or a cybersecurity professional for further assistance.
Prompt action can help mitigate the damage and prevent further unauthorized access.
Final Thoughts: Building a Culture of Security
Securing your mobile content is not just about using the latest technology—it’s about fostering a culture of security awareness. Regularly educating yourself and your team about best practices, remaining vigilant about potential threats, and consistently applying security measures will create a robust defense against cyber risks.
Remember, the goal is to maintain a proactive stance rather than a reactive one. By incorporating these practices into your daily routine, you’ll ensure that your mobile devices remain secure, protecting both your personal and professional data.
Empower yourself with the knowledge and tools to secure your mobile content effectively. With this guide, you’re well on your way to navigating the complexities of mobile security with confidence and ease.